The risk for identity fraud has never been greater. Tools like AI and deep fakes make it easier for criminals to impersonate and steal your information.
Although individuals and businesses should be concerned about these risks, businesses are responsible for protecting customers’ sensitive information. In fact, failing to comply can often result in hefty fines, damage to the company’s reputation, or a loss of customer trust.
One of the best ways businesses can protect their data is with an in-depth identity verification and authentication program. Using the latest digital identity verification tools lowers the risk of data breaches.
However, when it comes to verification vs authentication, know that these terms are similar but have distinct differences. Understanding these differences can help you build a safe and reliable ID verification process.
Understanding Identity Verification
Identity verification is crucial for securing your company’s data. So, here’s a detailed guide on how it works.
What is Identity Verification? (Definition and purpose)
Have you come across a website that says, ‘To access this information, please verify your identity’ – That is a perfect use case of identity verification.
The ID verification process confirms whether a person is who they claim to be, ensuring the authenticity of the individual’s claimed identity. This step provides an additional security layer, securing people’s identities and saving their accounts from vulnerabilities.
Verification is vital for online settings and brick-and-mortar stores. In both cases, customers’ personal data, including transactions and purchase history, are recorded in the system for better communication and customer interactions.
Methods of Identity Verification
Identity verification employs various verification methods to confirm and verify an individual’s identity, such as:
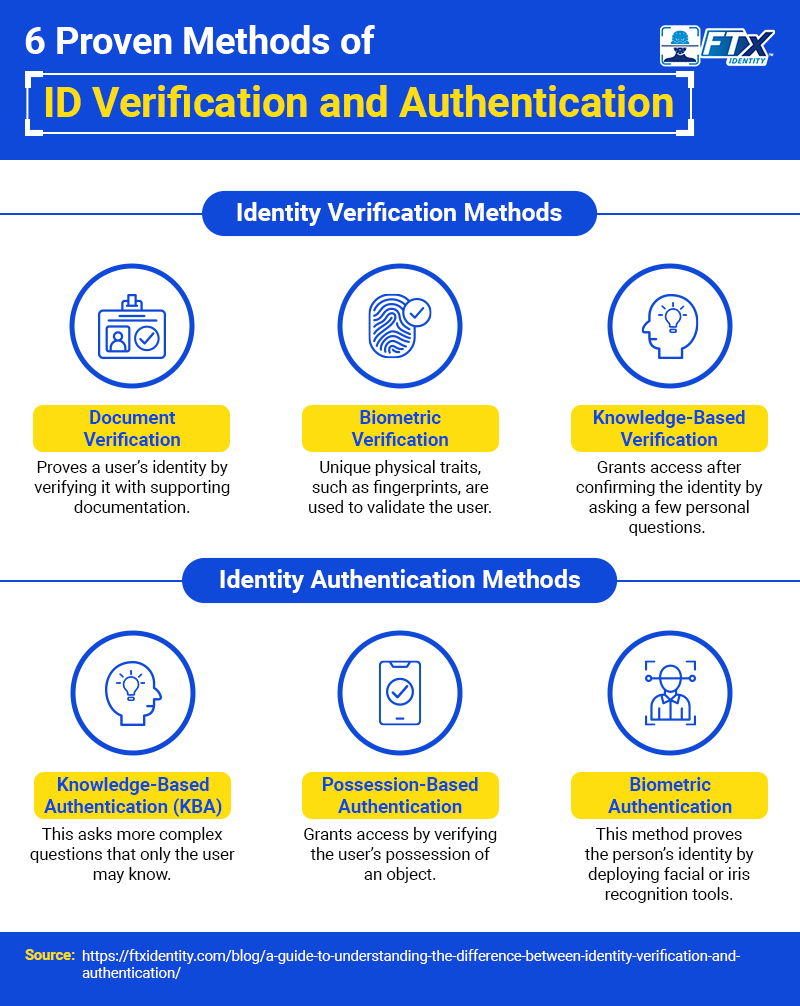
1. Document Verification
Identity document verification is a process that confirms a person’s identity by providing supporting documentation.
For example, immigration officers always ask for relevant documents before granting a visa, such as a passport, travel tickets, hotel booking, etc. Moreover, they ask many questions about the documents and their identity; this ensures the person is who they claim to be.
Other types of documents used in verifications are:
- Driver’s license
- Social security card
- National ID card
- Employment ID document
- Bank statements
2. Biometric Verification
The identity biometric verification process uses a person’s unique physical or behavioral traits to confirm their credentials. It matches the person’s document against their physical characteristics like iris, fingerprints, facial recognition, or voice patterns to confirm identity.
The most common uses cases of biometric identity verification include:
- Banking and financial institutions
- Age-restricted companies
- Mobile and web shopping portals
- Government agencies (such as law enforcement)
- Healthcare
- Retail sector
- Immigration offices
3. Knowledge-Based Verification
Knowledge-based verification (KBV) is widely used on online platforms as a two-step verification process. It generally starts with asking questions related to the user’s personal details. These questions validate a person’s identity and grant access to sensitive or financial information.
A few examples of knowledge-based verification are:
- What is the name of your first pet?
- What was your previous address?
- What is the name of your first school?
- What is your mother’s maiden name?
Knowledge-based verification is commonly used in industries such as:
- Ecommerce websites
- Age-restricted products (such as tobacco and cannabis)
- Banking and insurance companies
- Healthcare
Role in Fintech and Other Industries
Identity verification is pivotal in several industries, with a notable impact on Fintech. Grandview Research estimates that the identity verification market will grow at an annual rate of 16.7% between 2023 and 2030. A few of the examples of fintech identity verification are:
1. KYC (Know Your Customer) Regulations
In many industries, including Fintech, it is mandatory to adhere to KYC regulations. ID verification ensures financial institutions and other data-sensitive companies have complied with government regulations to provide accurate customer information and reduce the risk of fraudulent activities like money laundering.
It is a mandated step for:
- Opening a bank account
- Anti-Money laundering compliant
- Return and Acceptance of checkbook
- Loan processing
2. Identity Theft Prevention
Identity verification can help with preventing identity theft across various industries. It acts as a gateway and safeguards your personal data from getting into the wrong hands. Three crucial steps of identity theft prevention are:
- Do not disclose your personal information, and keep it secure
- Regularly monitoring your credit card and bank statements
- Restrict the use of public computers to access sensitive information
Methods of Identity Authentication
Here’s a list of a few of the common identity authentication methods, each offering unique advantages:
1. Knowledge-Based Authentication (KBA)
This identity authentication method validates a user’s identity through information only the user should know.
For example – Passwords, security questions, social security numbers, PINs, or personal questions.
To maintain higher security standards, there are mainly two types of KBA:
Static – They are a set of questions that users can select from various security questions. The only drawback with these questions is that anyone can learn their answers after a few interactions.
For example,
- Who was your childhood friend?
- Where was your last vacation?
Dynamic – These security questions are more specific, personal, and complex for fraudsters to answer. They are mainly real-time questions, and they are compiled based on the user’s public records or credit reports.
For example,
- In which of the following addresses did you previously reside?
- What car was registered to you in Rock Hill in 2010?
2. Possession-Based Authentication
As a two-factor authentication (2FA), possession-based authentication grants access by verifying the user’s possession of an object.
For example, security tokens on hardware devices like mobile devices
3. Biometric Authentication
The only difference between biometric authentication and verification is the level of security. While verification only confirms a person’s identity, authentication proves the person’s identity by deploying several authentication methods.
This method authenticates profiles based on their unique physiological or behavioral characteristics.
For example – Fingerprints, facial recognition, iris recognition, or audio check.
4. Multi-Factor Authentication (MFA)
This authentication method ensures that users enter two or more authentication steps to access the page or information to reduce the risk of unauthorized access.
For example, a combination of password and security questions OR Password and authorization link sent to email address.
Role in Cybersecurity
The role of identity authentication in cybersecurity is to flag and catalog fraudulent activities and profiles. Further, it records and authenticates the activities of the genuine ones. This way, each system gets notified of the red flags and how to avoid them. Identity authentication in cybersecurity serves in various ways, such as:
1. Protecting Accounts and Data
ID authentication methods protect the data by ensuring that only authorized individuals gain access to it. This identity verification method prevents unauthorized users, such as scammers, from phishing and compromising sensitive accounts and data.
2. Two-Factor Authentication (2FA)
2FA requires users to enter two separate authentication methods before granting access. This additional security layer protects companies against unauthorized access.
Identity Verification Vs. Authentication: Key Differences
| Key Difference | Identity Verification | Identity Authentication |
|---|---|---|
| Purpose | It confirms and validates a person’s identity with the presented information or documentation. | The user’s identity is matched with supporting data, such as biometrics, before granting access to systems. |
| Process | It cross-checks the user’s personal information or documents. | It utilizes methods such as MFA, 2FA, biometrics, or possession verification. |
| Level of Assurance | Any form of identity verification has high accuracy levels. | Identity authentication adds an extra layer of security, making it more popular, reliable, and unbreachable. |
| Regulatory Requirements | Identity verification tools must be compliant with industry regulations and KYC standards. | ID authentication requires the same as ID verification with additional data protection and cybersecurity regulations. |
| Access Control | It only verifies the document and the user’s identity. For example, train or flight ticket |
It has high scrutiny levels and authenticates users to grant or deny access to services based on ID confirmation. For example, granting visas and buying age-restricted products. |
| User Experience | Generally quick, less intrusive, and requires minimal document submissions | Can be lengthy and tedious, requiring more authentication method |
How Businesses Use Identity Authentication & Verification
The latest authentication and identity verification methods utilize technology and AI for better, more secure verification. Businesses use both types of identity checking in their operations for customers, access control, and employee verification.
1. Authentication Methods
Access Control: Businesses use identity authentication to control sensitive data and systems access. Employees are given unique login credentials and sometimes additional authentication factors to ensure that only authorized individuals can access certain information.
Financial Transactions: Banks and other financial institutions use identity authentication to verify the identity of users making transactions. This can involve multiple authentication factors, such as a password, a one-time code sent to a registered phone number, or a fingerprint scan on a mobile banking app.
Regulatory Compliance: Many industries have regulations requiring certain levels of identity authentication. For example, healthcare providers must authenticate users’ identities when accessing electronic health records to comply with HIPAA regulations.
2. Verification Methods
Customer Onboarding: Financial institutions like banks and insurance companies use identity verification during customer onboarding. They verify the identity of new customers against government-issued IDs and other documents to comply with Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations. This process helps prevent fraud and illegal activities.
Online Marketplaces: Online platforms such as e-commerce sites, ride-sharing services, and home-sharing services use identity verification to build trust and safety. For instance, a home-sharing platform may require hosts to verify their identity by uploading a government-issued ID or taking a selfie. This helps ensure that the person listing the property is who they claim to be, creating a safer environment for guests.
Telecommunications Companies: Telecom companies use identity verification when issuing SIM cards to customers. They verify the customer’s identity against a government-issued ID to ensure the SIM card is not being issued for fraudulent purposes. This is particularly important in countries where regulations require telecom companies to verify the identity of their customers.
Businesses and customers could be at risk because of the confusion between verification and authentication. Instead of giving two separate services, some solution suppliers combine the two, which furthers the misconception.
Identity verification tools can’t always guarantee that the person providing the identifying information is the true owner of it. A business becomes exposed to account takeover fraud and fake identities if it treats a verified identity (“the identity exists”) as authenticated or proofed (“the user is who they say they are”).
Security and Fraud Prevention
With most businesses working on digital platforms, it is crucial to safeguard digital transactions and sensitive data and prevent fraudulent activities. Robust security measures and identity verification software are imperative to secure your company’s data from:
1. Identity Verification for Fraud Prevention
Here are the top 4 ways to secure the company data from fraudulent and phishing activities:
- ID verifications act as a firewall against identity theft and fraud by confirming the legitimacy of an individual’s identity.
- Robust verification methods scrutinize identity documents and reduce the risk of malicious activities under false identities.
- Biometric verification adds an extra security layer, ensuring that individuals presenting their IDs are genuinely who they claim to be.
- It is crucial for sectors like finance and eCommerce, where the risk of data breaches is high.
2. Identity Authentication for Security
Here are the top 4 ways that identity authentication works to secure your company information:
- It safeguards sensitive data and acts as a gatekeeper protecting documents from unauthorized access.
- ID authentication adheres to regulatory compliance, industry regulations, and standards, ensuring the company is safe from legal obligations.
- It reduces the risk of unauthorized access, data breaches, and other security vulnerabilities.
- ID authentication ensures the overall security of the business.
How to Ensure Good Customer Experiences?
Ultimately, these safeguards shouldn’t ruin a good user experience. Customers will experience negative effects due to overly intrusive verification procedures, which could eventually result in customer churn.
Authentication procedures must be smooth to allow businesses to compete without suffering the adverse effects of a bad customer authentication experience.
According to a CMO Council study, 61% of customers indicate that their frustration with authentication has led them to abandon transactions they otherwise would have finished. Additionally, two-thirds of customers said they would switch businesses for a better digital experience, according to TransUnion’s 2022 Global Digital Fraud Trends Report.
Building Trust with Verification Technology
Identity verification and authentication are essential for businesses to maintain regulatory compliance, but they also contribute to trust building, creating the foundation for long-term customer relationships.
Customers are more inclined to trust your business with their personal, financial, legal, or medical information if they have confidence in your verification and authentication procedures. People are more inclined to continue the onboarding process and collaborate with you in the future if you use technologies that can quickly and accurately validate user data.
The business must ensure that customers interact safely and in a way that promotes trust without compromising the customer’s experience. For the best protection of customers, to prevent significant fraud losses, and to guarantee a frictionless customer experience, businesses must implement identity verification and authentication processes.
The Future of Digital Verification and Authentication
Digital identity verification is what the future holds.
Customers are now eager to exchange digital identification documents with businesses that can protect their data efficiently, and many governments are experimenting with IDs like digital licenses and ID cards. As a result, how websites verify age is becoming more sophisticated, and age-checking tools online are now commonplace.
However, it doesn’t come to a halt there. The next generation of digital ID verification and authentication technologies will also use extra information like the user’s location and normal behaviors to confirm ID more successfully and combine cutting-edge algorithms to give real-time verification results.
Demo FTx Identity Today
A unified login authentication and authorization system, identity management, and seamless age verification are all provided by FTx Identity. We understand that choosing one from verification vs authentication is challenging, but here at FTx, you will be guided by experts who can help you decide!
Our user-friendly platform is suitable for businesses of different shapes and sizes and industries of all kinds—everything from grocery stores and gyms to tattoo parlors and nightclubs. At FTx Identity, we understand that the safety and security of your business and customers are paramount. Here, we also protect you from online ID verification fails.
That’s why you can count on us to provide reliable support throughout every stage! Ready to learn more about us? Get in touch with one of our specialists today to set up a consultation and demo!
Keep learning. See our guide Identity Theft vs Identity Fraud to learn more about identity security.
