It is becoming more challenging to create trust in the virtual world with the rise of cyber threats. Identity verification needs to be a main priority in protecting both customer privacy and business assets.
The stakes are high. According to Cybercrime Magazine, it was estimated that cybercrimes would cause businesses to suffer devastating losses of approximately $10.5 trillion by 2025. That breaks down to an astonishing average of $20 million per minute.
Ignoring this reality is no longer an option.
Knowledge is the best way to avoid cybercrime. That’s why we’re exploring the top cybersecurity trends for 2026.
Keep reading for advice on navigating the ever-shifting threat landscape. We cover different types of cyberattacks and their profound economic impact, helping you build a proactive security strategy.
Top Cybersecurity Trends for 2026
The biggest trend in cybersecurity is the use of technology. Using advanced technology can help safeguard both your business and customers.
Here are the top trends you should be focusing on:
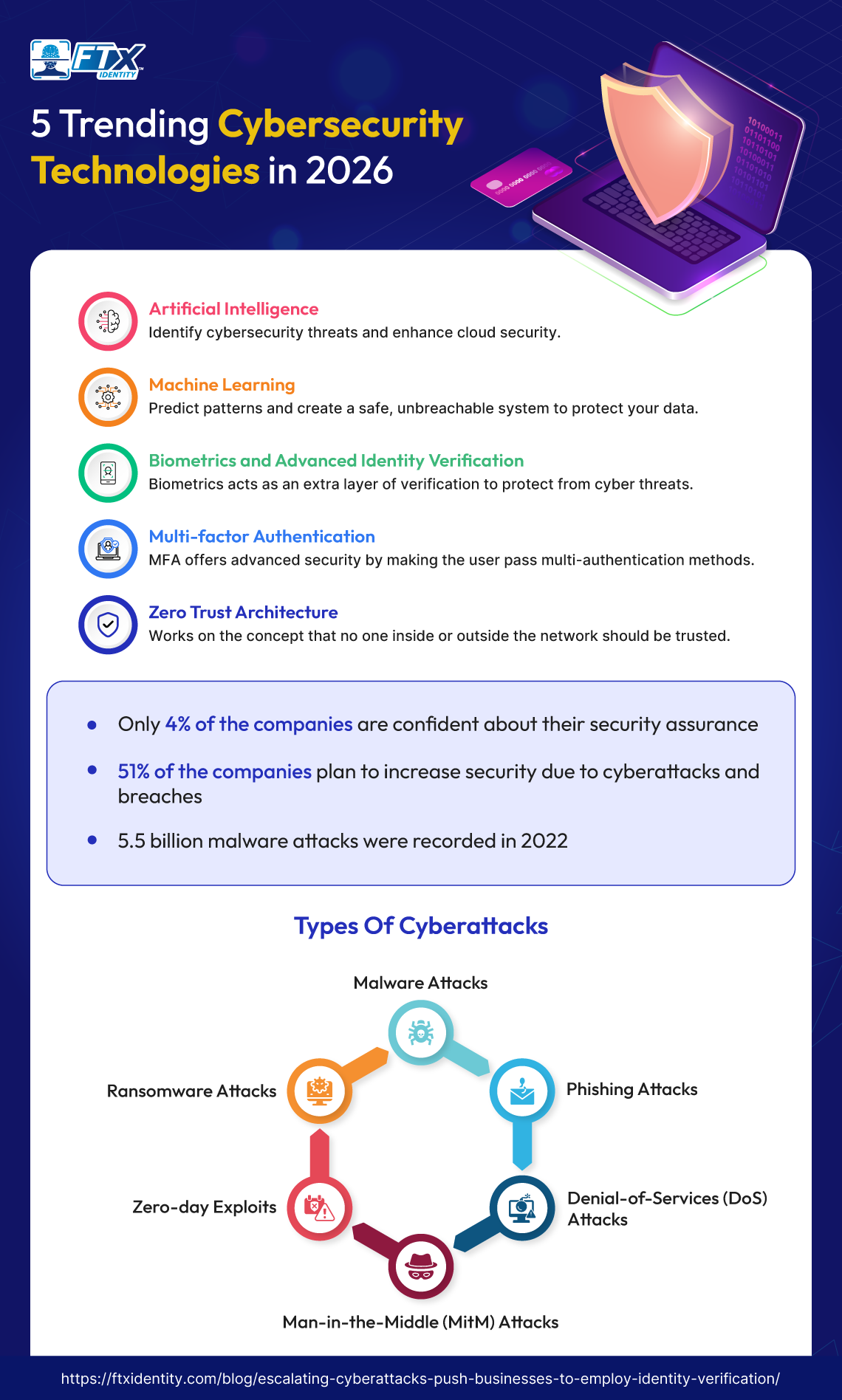
Artificial Intelligence and Machine Learning (ML) in Cybersecurity
Artificial intelligence (AI) has the potential to enhance cloud security by using advanced algorithms to quickly analyze large datasets and identify emerging threats. Additionally, AI can predict attack patterns, strengthening proactive defense measures.
Zero Trust Architecture
Zero trust is built on the principle that nobody, whether they are inside or outside the network, should be considered trustworthy without undergoing a comprehensive identification process.
Quantum-Resistant Cryptography
Quantum computing isn’t breaking transport layer security (TLS) tomorrow—but smart teams are planning for the day when today’s encryption is no longer enough. Reports from major consultancies and vendors are clear: quantum will eventually undermine current public-key cryptography.
That’s pushing organizations to:
- Inventory where long-lived secrets and archives live
- Test emerging cybersecurity technologies like post-quantum algorithms
- Build crypto agility into systems so algorithms can be swapped without rewriting everything
If your business depends on long-term cybersecurity and data protection (think healthcare records, intellectual property, and legal archives), post-quantum readiness is no longer a niche research and development project—it’s a multi-year migration path that should already be on your roadmap.
Identity Security and Passwordless Authentication

If zero trust is the skeleton, identity is the spine. Most of the biggest cybersecurity threats today begin with compromised credentials, not zero days. That’s why 2026 is the year identity security and passwordless authentication go from “future” to “normal.”
We’re already seeing:
- Large platforms making passkeys the default (Microsoft, Apple, Google)
- FIDO2/WebAuthn adoption in consumer and workforce login flows
- Stronger identity verification to combat synthetic identities and account takeover
Passwordless doesn’t just clean up user experience (UX). It directly addresses one of the nastiest cybersecurity concerns: credential reuse and phishing. Combined with risk-based policies and device trust, it turns identity into one of the highest-signal cybersecurity areas you have.
Growth of Cloud Security & Multi-Cloud Protection
Most enterprises are now multi-cloud whether they wanted to be or not. That reality is driving specific cybersecurity trends:
- Broader adoption of cloud-native application protection platform (CNAPP), cloud security posture management (CSPM), and data security posture management (DSPM) to watch cloud posture and data exposure.
- Stronger identity and access governance across Amazon Web Services (AWS), Azure, Google Cloud Platform (GCP), and software as a service (SaaS).
- More investment in application programming interface (API) security as microservices and integrations multiply.
The emerging threats here are less about a single misconfigured simple storage service (S3) bucket and more about inconsistent policies and fragmented identities across clouds. Multi-cloud identity orchestration, shared policy models, and unified observability are becoming non-negotiable if you care about consistent cybersecurity and data protection.
Ransomware 3.0
Ransomware has evolved far beyond “encrypt and demand.” Recent data shows that most modern campaigns involve data theft before encryption, turning nearly every serious incident into both an outage and a breach.
What some are calling “Ransomware 3.0” typically includes:
- Double or triple extortion (encryption + exfiltration + public shaming)
- Targeting of hypervisors, backups, and cloud workloads
- Attacks on critical sectors like healthcare, finance, and supply chains (AP News)
This remains one of the top cybersecurity threats, and it’s driving more investment in:
- Immutable backups and isolated recovery
- Granular segmentation so a single compromised endpoint can’t flatten an environment
- Playbooks that assume partial compromise and prioritize resilience over perfection
Supply Chain Cybersecurity
Attackers don’t need to batter your front door if they can walk in through a trusted partner. That’s why supply chain cybersecurity continues to sit near the top of boardroom cybersecurity concerns.
Think:
- Compromised software updates
- Tampered libraries and build pipelines
- Third parties with over-privileged virtual private network (VPN) or API access
Organizations are reacting by:
- Demanding software bill of materials (SBOMs) and security attestations from vendors
- Monitoring third-party access more tightly
- Treating integrators, managed service providers (MSPs), and SaaS providers as part of their threat model
Supply chain risk is no longer just an IT problem; it’s a core part of vendor selection and contract negotiation.
Human-Centric Cybersecurity

For all the talk about emerging cybersecurity technologies, humans are still involved in most breaches—clicking, approving, misconfiguring, or being socially engineered.
“User awareness training” isn’t enough on its own. The shift is toward human-centric cybersecurity:
- In-context warnings in tools where people actually work (email, chat, browsers)
- Adaptive training tailored to roles and behavior
- Processes designed so the safe path is the easiest one
Instead of treating employees as the “weakest link,” leading teams design controls around human behavior. It’s one of the subtler but important evolving cybersecurity strategies for 2026.
What Is a Cyberattack?
A cyberattack is any digital crime in which a fraudster tries to deliberately gain unauthorized access to a computer system, network, or digital device. This includes obtaining sensitive information, such as personal and financial data.
Criminals use various tactics like malware attacks and social engineering scams to gain unauthorized entry into their desired systems.
Types of Cyberattacks
Cyberattacks come in various types, each using different methods to achieve specific goals.
Below are several examples:
Malware Attacks
Malicious software is called malware. It is considered an umbrella term for any form of malware. Examples include MITM attacks, phishing, and ransomware.
An attack causes damage or harm to a computer, server, or computer network to steal data or money. Malware can either infect multiple devices or stay dormant within a single device, harming only the device it occupies.
Phishing Attacks
“Phishing” involves attempting to gain access to personal information, like usernames, passwords, and bank account details, with the intention of either using or selling the acquired data.

The attacker uses a deceitful tactic, presenting themselves as a reputable source, to entice and deceive the victim.
An example would be sending an email to a victim saying that they won a gift card and to provide sensitive information to claim it.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
A denial of service (DoS) attack occurs when a criminal floods a specific host or network with excessive traffic, rendering it unable to respond or causing it to crash. This results in the denial of access to legitimate users.
Similarly, a distributed denial of service (DDoS) attack aims to exhaust the resources of a system. However, in a DDoS attack, the attacker controls many malware-infected host machines.
These attacks are named “denial of service” because they prevent the victim’s site from providing services to those seeking access to it.
Man-in-the-Middle (MitM) Attacks
An attacker places themselves between two parties who believe they are communicating directly, allowing the attacker to intercept and change the data being transmitted.
This poses a major risk to online security as it allows the attacker to obtain and manipulate sensitive information in real-time, such as login information and credit card details.
Zero-Day Exploits
The technique involves exploiting a software vulnerability that is not yet known to the developer or security researchers.
Due to the recent discovery of the vulnerability, there are currently no immediate security measures in place. There was no time to address and fix the vulnerability.
These attacks pose a challenge in cybersecurity as they allow criminals to infiltrate networks without being detected.
Ransomware Attacks
These attacks involve holding a user’s or business’s files hostage and demanding money until payment is made. Once it is paid, the victim is provided with instructions on how to regain access to their files that have been encrypted.
During an attack, the ransomware is downloaded by the victim, either from a website or through an email attachment. This malware targets unaddressed vulnerabilities in the system that have been overlooked by both the manufacturer and the IT team.
The Economic Impact of Cyberattacks
The economy can experience major setbacks as cyberattacks become more common in the ever-changing digital landscape, including in the following ways:
Financial Losses
Cyberattacks can result in financial blows for businesses.
These attacks can jeopardize valuable assets such as credit card information and intellectual property, which can be traded illicitly. This results in major financial harm to both businesses and customers alike.
They can also result in a delay in regular business operations, which can lead to missing deadlines and losing relationships with customers.

Reputational Damage
The aftermath of a cyberattack can result in a loss of trust from customers, investors, and partners, causing them to distance themselves from a business.
Additionally, when a cyberattack receives a lot of media coverage, a business may be seen as unsafe and untrustworthy, which can result in damaging its reputation.
Insurance and Recovery Costs
Businesses are growing more concerned than ever about the threat of cyberattacks. However, the cost of insurance policies has significantly increased due to the rising number and severity of these attacks.
Insurers are more selective in determining who and what qualifies for coverage due to the unpredictable nature of future risks.
Bringing in cyberattack experts to fix the damage caused can also be extremely costly, between containing the attack and collecting evidence.
The process of fixing compromised systems, recovering lost data, and repairing damaged infrastructure can lead to significant expenses for hardware, software, and specialist services.
Job Losses and Economic Slowdown
Cyberattacks can have severe consequences for businesses, including operational disruptions and financial losses. As a result, downsizing may be a possibility, leading to job losses for employees.
Attacks targeting critical infrastructure or major corporations can cause significant damage to the global supply chain. Disruptions in the supply chain can result in shortages and increased prices for goods and services.
Industry-Specific Cybersecurity Trends
The core building blocks—identity, AI, and cloud—are shared. But the way emerging threats play out looks very different in each sector.
Retail & eCommerce
Retail and eCommerce sit where payments, personal data, and high-volume web traffic meet. Their cybersecurity concerns center around:
- Payment fraud and account takeover
- Bot and scraper mitigation
- Web app and API security for storefronts and marketplaces
Here, AI cybersecurity tools are used heavily in fraud analytics and behavioral scoring, blurring the line between “security” and “payments risk.” A single breach doesn’t just hurt ops—it erodes consumer trust overnight.
Banking & Fintech
For banks and Fintechs, security is part of the product’s promise. This sector sees some of the biggest cybersecurity threats by volume and sophistication.
Key trends:
- real-time transaction analysis powered by machine learning security
- stronger controls around APIs and embedded finance platforms
- layered defenses for real-time payments and open banking ecosystems
They’re often early adopters of new emerging cybersecurity technologies, from AI-based fraud detection to continuous authentication, because the cost of failure is measured directly in money and regulatory pain.
Healthcare
Healthcare carries a unique mix: extremely sensitive data, life-critical systems, and often underfunded IT. That cocktail makes it a prime target in recent cybersecurity attacks and one of the top cybersecurity threats from a societal point of view.
Trends include:
- strict focus on cybersecurity and data protection around electronic health records (EHRs) and clinical systems
- segmentation of clinical networks from corporate IT and guest networks
- emphasis on incident response because ransomware can now delay care, not just billing
The question here isn’t just “Did we lose data?” but “Did security impact patient outcomes?”
Telecom & Tech
Telecom and tech companies run much of the world’s connectivity and infrastructure, so their cybersecurity areas include national-level risk.
We’re seeing:
- More focus on 5G core and edge security
- Protection of SaaS and platform APIs from abuse
- Securing AI and ML pipelines themselves from model theft and poisoning
Because they sit upstream of many other industries, their emerging threats often cascade. That makes resilience and transparency especially important here.
Challenges in Adopting the Latest Cybersecurity Trends

All of this sounds great in a trends report. In reality, most teams are dealing with tight budgets, legacy systems, and too many tools. Let’s talk about the gap between aspiration and execution.
High Implementation Costs
Zero trust rollouts, AI-driven detection, and post-quantum migration—none of these are cheap. Security leaders have to justify spending in the context of:
- Reduced risk from top cybersecurity threats
- Avoided downtime and regulatory penalties
- Alignment with broader digital transformation
The trick is sequencing: prioritize controls that reduce the most critical cybersecurity concerns first, instead of chasing every shiny tool.
Skill Shortages and Talent Gaps
The demand for skilled defenders far outpaces supply. Cloud, AI, identity, and incident response skills are especially scarce.
That leads to:
- Overloaded security operations centers (SOCs)
- Under-tuned tools generating noisy alerts
- Dependence on managed security service providers (MSSPs) without internal ownership
It’s one reason emerging cybersecurity technologies increasingly ship with automation, guided workflows, and AI copilots—to make senior expertise go further instead of burning people out.
Legacy System Compatibility
Almost every organization has a long tail of legacy apps and infrastructure. They’re critical, hard to modernize, and often not designed for modern authentication or monitoring.
This complicates:
- Zero Trust (no native identity hooks)
- Visibility across environments
- Upgrades to quantum-resistant crypto schemes
Security teams end up building wrappers, proxies, and compensating controls—slowing adoption of the latest cybersecurity trends.
Complexity of Modern Security Tools
Tool sprawl is a quiet problem. Organizations buy multiple overlapping platforms—each with dashboards, alerts, agents, and connectors. The result is often:
- Analysis paralysis
- Conflicting signals
- Gaps between tools where emerging threats can slip through
Consolidation, careful platform choices, and clear ownership are becoming just as important as buying new tech.
Cyber Threats Evolving Faster Than Adoption
Attackers don’t wait for your next budget cycle. We’ve seen recent cybersecurity attacks evolve from simple ransomware to data-theft extortion, supply chain compromises, and AI-augmented social engineering in just a few years.
That pace means:
- Once-a-year risk assessments feel outdated
- Long, multi-year security projects may miss the current threat model
- Continuous adaptation is more valuable than big one-off deployments
This is where evolving cybersecurity strategies matter: small, frequent improvements guided by threat intel and real incident data.
Compliance Overload
Finally, regulation is catching up. Data protection, AI governance, sector-specific rules—keeping up is a job by itself.
The trap is treating compliance as the finish line. You can be “compliant” and still be vulnerable to very real, very current emerging threats. The more mature approach is to:
- Map controls to actual top cybersecurity threats
- Use compliance as a floor, not a ceiling
- Align audits with the reality of how people and systems work
Wrapping Up
It is clear that cybersecurity is an ever-evolving field, and staying informed about the latest trends and threats is crucial for individuals and organizations alike.
From the rise of cyberattacks through social engineering to the increased use of artificial intelligence in detecting and preventing breaches, there are numerous developments shaping the landscape of cybersecurity.
It is important to continue to educate ourselves and invest in cutting-edge technologies to effectively combat these ever-growing threats. As we navigate this digital age, it’s important to remember that our actions also play a role in maintaining our online safety.
Stay Ahead of Cyber Threats
Cyber threats aren’t slowing down—and neither should your defenses. Reach out to FTx Identity to schedule a consultation and demo, and see how our identity verification solutions can help protect your business and your customers.
