Let’s be honest—proving who you are online shouldn’t be this complicated.
In a digital-first world, businesses need to verify customers quickly, securely, and without adding friction. At the same time, customers expect fast, seamless experiences (and don’t want to upload their ID five different times just to get through a checkout or sign-up process).
According to a PYMNTS and Trulioo report, more than half of companies lose customers to onboarding drop-offs caused by friction.
The problem? Most traditional identity methods—like passwords, document uploads, or manual verification—just don’t cut it anymore. They’re easy to fake, vulnerable to breaches, and often slow everything down.
That’s where verifiable digital credentials (VDCs) come into play.
In this blog post, we’ll break down what verifiable digital credentials are, how they work, and why they’re quickly changing the way businesses verify identity—making the process faster, safer, and far less frustrating for everyone involved.
What Are Verifiable Digital Credentials (VDCs)?
Let’s break it down.
What are verifiable digital credentials, and why are so many businesses starting to rely on them?
Definition and Core Concept
At a high level, verifiable digital credentials are secure, digital versions of things you already use to prove who you are—like IDs, licenses, or certifications.
But here’s the key difference: they’re cryptographically secured, which means they can be instantly verified as authentic and haven’t been tampered with.
Instead of uploading documents or waiting for manual approval:
- A trusted authority (like a government, bank, or employer) issues the credential
- You store it securely (usually in a digital wallet)
- You share it when needed—quickly and securely
Simple, right?
Key Components of VDCs
To understand how verifiable credentials work, it helps to break them down into four core roles.
Issuer
The issuer is the trusted organization that creates and digitally signs the credential—like a government issuing an ID or a bank verifying a customer. This digital signature is what makes the credential authentic and tamper-proof.
Because the credential is cryptographically signed, its validity can be confirmed instantly. There’s no need to manually check with the issuer every time, which significantly speeds up the verification process.
Holder
The holder is the individual who receives and owns the credentials. Instead of having businesses store and manage their data, the holder simply keeps credentials securely in a digital wallet.
This puts the user in control. They can choose what information to share, when to share it, and who gets access—eliminating the need to repeatedly upload or expose unnecessary personal details.
Verifier
The verifier is the business or platform requesting proof of identity or eligibility. This could be for age verification, account setup, or regulatory compliance.
With verifiable credentials, the verifier can instantly validate the information using built-in cryptographic proofs—no manual review needed. This reduces fraud risk while creating a faster, smoother experience for customers.
Credential Data
Claims are the specific pieces of information inside the credential, such as name, age, or qualifications. These are the actual data points being shared during a verification request.
What makes VDCs powerful is selective disclosure. Instead of sharing an entire document, users can share only what’s necessary—helping protect privacy while still meeting verification requirements.
Difference Between Digital Credentials and Verifiable Credentials
To really see the difference, it helps to compare verifiable credentials with traditional digital credentials and how each one handles trust, security, and verification.
Static vs. Cryptographically Verifiable
Most digital credentials today are basically just digital copies of paper documents—think PDFs, scanned IDs, or uploaded images. They get the job done, but they’re still static files.
That means they can be edited, faked, or end up stuck in a manual review queue while someone double-checks them.
Verifiable credentials take a much smarter approach. Instead of being just an image or file, they’re digitally signed and cryptographically secured. In simple terms, they’re built in a way that lets systems instantly confirm, “Yep, this is real,” without needing a human to step in.
Trust Model Comparison
Here’s where the real mindset shift happens in practice.
Traditional systems are built on layers of trust that sit outside the data itself—someone has to review documents, or a platform has to rely on a central database being accurate and up to date.
With verifiable credentials, that trust is built right into the credential itself. The verification sn’t about guessing or double-checking—it’s about instantly confirming authenticity through cryptography.
No back-and-forth, no manual checks, just a clear yes or no.
Example Scenarios
Once you look at it side by side, the difference really starts to click into place:
- Uploading an ID and waiting for approval vs. instantly sharing a verified digital ID
- Filling out the same forms repeatedly vs. sharing pre-verified information in one step
- Waiting minutes—or even hours—for verification vs. getting approved in seconds
It’s a simple shift, but it completely changes the user experience—from slow and manual to fast and seamless.
Key Standards Behind Verifiable Digital Credentials
Behind the scenes, there are a few global standards that help make verifiable credentials secure, interoperable, and scalable.
1. W3C Verifiable Credentials Data Model
The W3C Verifiable Credentials Data Model is basically the foundation that defines how credentials are created, structured, and shared. It sets the rules for what a credential looks like and how it should behave when it’s issued or verified.
Because of this standard, different systems don’t have to reinvent the wheel or build custom formats. Instead, they can rely on a shared structure that ensures credentials issued in one system can be understood and verified in another—no matter the platform or provider.
2. Decentralized Identifiers (DIDs) Standard
Decentralized Identifiers, or DIDs, are what make user-controlled identity possible. Instead of relying on a central authority or database to manage identity, DIDs create unique digital identifiers that belong directly to the user.
This shift is important because it reduces dependency on centralized systems and gives individuals more control over their identity. In practice, it means users aren’t locked into one provider—they can carry their identity across services securely and seamlessly.
3. ISO and Regulatory Frameworks
Standards from organizations like the International Organization for Standardization (ISO) help bring consistency and trust to digital identity systems at a global level.
For example, ISO/IEC 18013, which supports mobile driver’s licenses, defines how digital IDs should be securely stored, shared, and verified.
These frameworks are especially important for real-world adoption because they help ensure verifiable credentials meet strict security and compliance requirements. They also help different countries and industries align on how digital identity should work in practice, which is key for global usability.
4. OpenID and Identity Protocols
OpenID Connect and OAuth are widely used identity protocols that already power most modern login systems. Their role in verifiable credentials is to help bridge the gap between new credential systems and existing authentication infrastructure.
In short, they make it easier for businesses to adopt verifiable credentials without completely rebuilding their login or identity systems. This allows credentials to be integrated into familiar workflows like sign-ins, account creation, and authentication flows.
Key Use Cases Across Industries
Verifiable digital credentials aren’t just theoretical—they’re already transforming how industries handle identity and compliance:
1. Financial Services (KYC & AML)
In financial services, identity verification is essential—but often repetitive and time-consuming. Customers are frequently asked to go through KYC (Know Your Customer) and AML (Anti-Money Laundering) checks every time they open a new account or interact with a new provider.
With verifiable credentials, users can reuse pre-verified identity information instead of starting from scratch each time. This not only speeds up onboarding but also reduces fraud risk and helps financial institutions maintain compliance more efficiently.
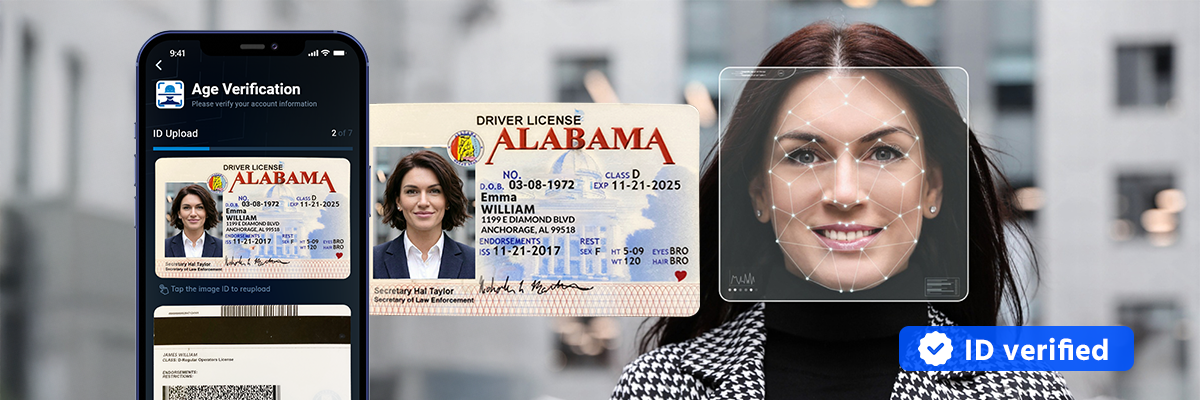
2. iGaming & Online Gambling
In the iGaming space, age and identity verification are critical for regulatory compliance. Operators need to ensure users meet legal age requirements while also preventing fraudulent accounts.
Verifiable credentials make this process a lot faster and more reliable in practice. Instead of manual ID checks or document uploads, users can instantly confirm their age or identity through a trusted digital credential. This helps platforms stay compliant while keeping the user experience smooth and friction-free.
and why it matters for compliance— we break it down in a practical way in our blog post.
3. Retail & E-Commerce
For retailers selling age-restricted products, verification is often a point of friction at checkout. Traditional methods can slow down transactions and create drop-off points for customers.
Verifiable credentials streamline this by allowing instant eligibility checks. Customers can prove they meet age or purchase requirements without submitting documents or waiting for manual approval, making the checkout process faster and more seamless.
4. Education & Hiring
Educational institutions and employers often face delays when verifying degrees, certifications, and work history. Fake credentials and slow verification processes can also add unnecessary complexity to hiring.
With verifiable credentials, academic achievements and professional certifications can be confirmed instantly. This reduces the need for lengthy background checks and helps employers make faster, more confident hiring decisions.
5. Government & Public Services
Governments are increasingly exploring digital identity systems to improve access to public services. Traditional processes often involve paperwork, in-person verification, and long processing times.
Verifiable credentials can simplify this by enabling secure digital IDs that allow citizens to access services more easily. At the same time, they improve security and reduce the risk of identity fraud within public systems.
Benefits of Verifiable Digital Credentials
Verifiable digital credentials create value across the whole ecosystem—from retailers and customers to regulators.
Instead of slow, manual verification processes, they enable a faster, more secure, and more user-friendly way to handle identity.
For Retailers
For retailers, the biggest benefit is reducing friction without sacrificing security. Verifiable credentials help cut down on fraud while removing the need for manual ID checks or document reviews.
They also speed up onboarding and checkout, which means fewer drop-offs and smoother customer experiences. Over time, this leads to stronger trust and better conversion rates.

For Customers
For customers, it all comes down to control and simplicity. They no longer need to repeatedly upload IDs or fill out the same forms across different platforms.
Instead, they can securely store credentials and share only what’s needed—nothing more. That means faster verification and better privacy at the same time.
For Regulators
For regulators, verifiable credentials make compliance easier to manage and enforce. Verification becomes more consistent because it’s backed by cryptographic proof rather than manual checks.
It also improves oversight and auditability, helping reduce fraud while maintaining clear, reliable verification standards across systems.
Key Technologies Behind Verifiable Credentials
To really understand how verifiable digital credentials work under the hood, it helps to look at the core technologies powering them.
These are the building blocks that make credentials secure, portable, and privacy-friendly—while still keeping verification fast and reliable.
1. Decentralized Identifiers (DIDs)
DIDs give users control over their digital identity without relying on a central authority or single provider. Instead of one organization owning and storing all identity data, the identity is user-owned and can be used across multiple platforms.
This makes it much easier for people to carry a trusted identity from one service to another without having to repeatedly recreate or re-verify who they are. It also reduces dependence on centralized systems that can become bottlenecks or points of failure.
2. Blockchain and Distributed Ledger Technology (DLT)
Blockchain and other distributed ledger technologies help strengthen trust by making records transparent, secure, and tamper-resistant.
They help ensure that once a credential is issued or verified, it can’t be quietly changed or manipulated after the fact. This adds an extra layer of integrity to the system and helps build confidence in the authenticity of the data being shared.
3. Zero-Knowledge Proofs (ZKPs)
Zero-knowledge proofs are really about proving something is true without revealing the underlying personal data. Instead of sharing full information, users can provide just the proof that a requirement is met.
For example, someone can confirm they are over 21 without exposing their exact date of birth or other sensitive details. This keeps verification both secure and privacy-friendly, which is especially important in regulated industries.
4. Digital Wallets
Digital wallets act as the secure storage layer for verifiable credentials. They allow users to store identity information in one place and manage it directly from their device.
When verification is needed, credentials can be shared instantly from the wallet without uploading documents or going through manual checks. This keeps the process smooth, fast, and much more user-centric.
Conclusion
At the end of the day, verifiable digital credentials solve a pretty big problem: how do you prove identity online without slowing everything down or compromising security in the process?
By replacing outdated, manual processes with secure, instant verification, VDCs make life easier for businesses—and a lot less frustrating for users.
As more industries move toward digital-first experiences, this isn’t just a “nice to have” anymore—it’s quickly becoming the new standard for identity verification.
every step of the customer journey.
